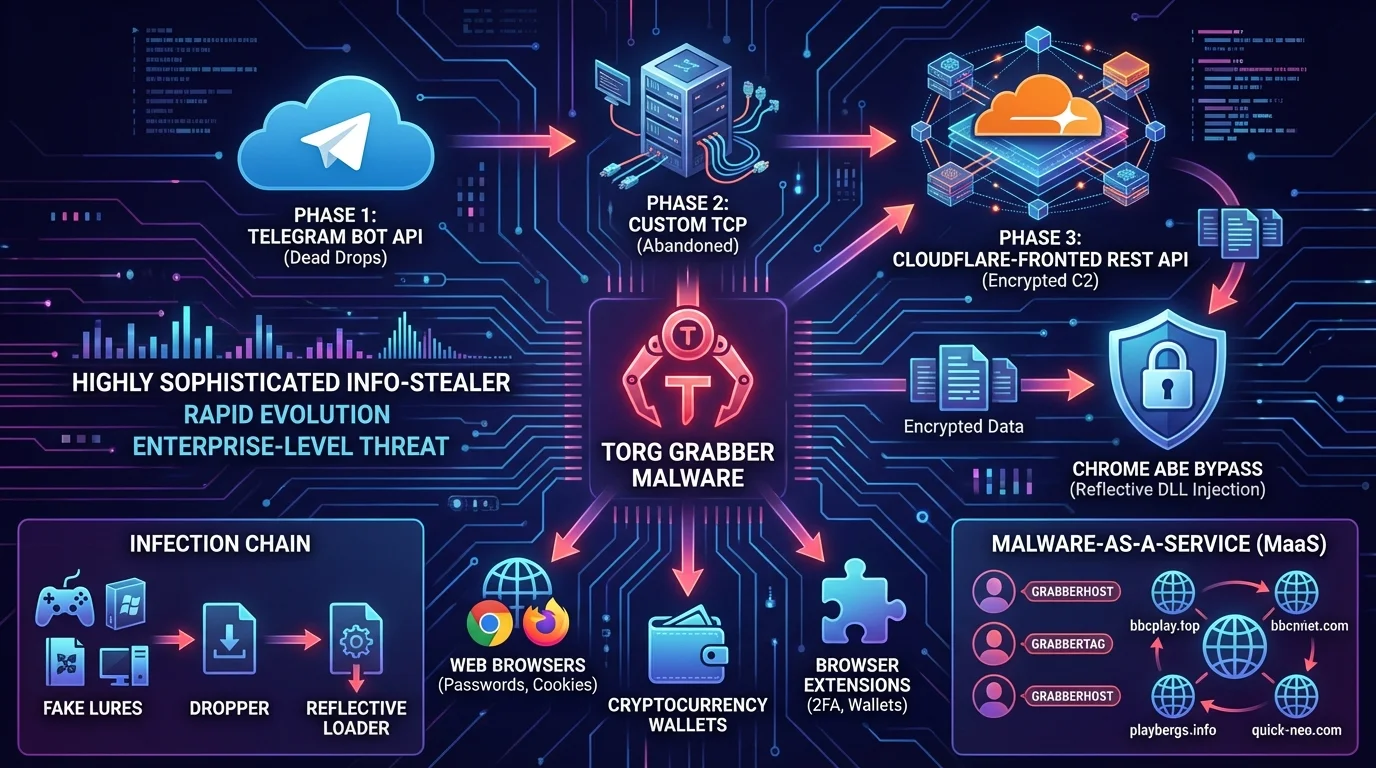
Cybersecurity researchers have uncovered a rapidly evolving information-stealing threat known as Torg Grabber malware, which has abandoned simple Telegram-based data exfiltration in favor of a highly sophisticated, Cloudflare-fronted REST API. Initially misidentified as a variant of the Vidar stealer, a 747 KB 64-bit sample revealed an internal "grabber v1.0" debug string, prompting a deeper investigation. Telemetry indicates that the malware iterated through three distinct data theft stages in rapid succession to optimize its operations.
Phase one, active from December 9 to 11, 2025, relied on Telegram Bot API dead drops, sending zipped data via the sendDocument function to private channels identified by hardcoded tokens. A short-lived second phase between December 17 and 20 experimented with a custom TCP protocol directed to the.tara.net.bd domain on port 50443. However, developers quickly abandoned this approach after only four builds, likely due to the operational complexity of managing it at scale.
By December 18, the malware family standardized on an HTTPS REST API command-and-control (C2) infrastructure. This final iteration utilizes endpoints such as apiauth and apiuploadchunk, securing payloads with ChaCha20 encryption and HMAC-SHA256 request authentication. These communications are routed through Cloudflare-protected domains, such as technologytorg.com, allowing the malware to fingerprint the host system and stream exfiltrated data in encrypted chunks.
Infection Chain and Chrome ABE Bypass
Torg Grabber is distributed via a multi-stage loader chain hidden inside lures like fake game cheats and pirated installers, with files often named similarly to "Terraria1.4.5.zip". The dropper propagates operator-specific settings via environment variables like GRABBERHOST and GRABBERTAG. A self-extracting loader then injects a 683 KB PE stealer directly into memory, keeping the core threat off the disk and allowing a single compiled stealer to be reused across multiple customers.
A critical capability of Torg Grabber is its 20 KB ChaCha20-encrypted reflective DLL, designed specifically to bypass Chrome's Application Bound Encryption (ABE). The malware abuses browser elevation COM interfaces to extract the AES-256 master key from within a trusted browser process. It then returns the key via a named pipe to decrypt protected logins and cookies seamlessly.
The stealer casts a wide net, targeting 25 Chromium-based browsers, 8 Firefox-family browsers, and 30 desktop cryptocurrency wallets. It also features hardcoded support for 850 browser extensions, which includes 728 cryptocurrency wallets and 103 password or 2FA extensions. In certain campaigns, it scavenges JSON output from a separate credential tool dubbed Underground, absorbing any leftover data.
Infrastructure and Malware-as-a-Service
Researchers mapped at least 18 C2 domains over a 12-week period, noting clear domain rotation chains such as gogenbydet.cc to bbcplay.top and playbergs.info. A parallel backend was also discovered on domains like quick-neo.com and 50elk.com, indicating that the developers are using modular, swappable C2 panels under a common codebase.
Analysis of 334 samples revealed more than 40 unique operator tags, confirming that Torg Grabber operates as a Malware-as-a-Service (MaaS). Open-source intelligence (OSINT) linked at least eight customers to Russian-language cybercrime accounts, with four utilizing Telegram Premium, reinforcing the commercial nature of this builder-and-panel combination.
How to Detect and Block Torg Grabber
With daily new builds and an expanding encrypted REST API C2 stack, security teams must move beyond simple domain blocklists. Defenders should prioritize the following actionable measures to protect their networks:
- Inspect TLS traffic for suspicious REST-pattern requests directed at specific paths like apiauth and apiuploadchunk.
- Monitor endpoint environments for the creation of specific configuration markers, particularly the GRABBERHOST and GRABBERTAG environment variables.
- Deploy advanced endpoint detection and response (EDR) rules to catch reflective DLL injections that attempt to abuse browser COM interfaces for ABE bypass.
My Take
The rapid evolution of Torg Grabber from a basic Telegram exfiltration tool to a Cloudflare-fronted REST API powerhouse in just weeks highlights a significant shift in the MaaS landscape. Cybercriminals are clearly recognizing that Telegram Bot API dead drops, while convenient and cheap to set up, lack the scalability, reliability, and stealth required for enterprise-level data theft operations.
By implementing a modular C2 framework and successfully bypassing Chrome's Application Bound Encryption (ABE), the developers behind Torg Grabber are positioning it as a premium alternative to established stealers. The discovery of 18 distinct C2 domains and a parallel backend proves this is a well-funded operation built for long-term resilience, rather than a quick cash grab.
For enterprise security teams, this signals the death of simple indicator-of-compromise (IoC) blocking. When malware can dynamically rotate through domains like bbcplay.top and playbergs.info while hiding behind legitimate Cloudflare infrastructure, behavioral detection and strict COM interface monitoring become the only viable lines of defense against modern info-stealers.