Table of Contents
The critical React2Shell vulnerability is currently being weaponized at an unprecedented scale, leaving over 900 companies compromised by automated attacks. If your infrastructure relies on React Server Components or Next.js, your environment variables and cloud credentials are at immediate risk of extraction. Hackers have streamlined this massive operation by combining AI orchestration tools with Telegram bots to track successful breaches in real time.
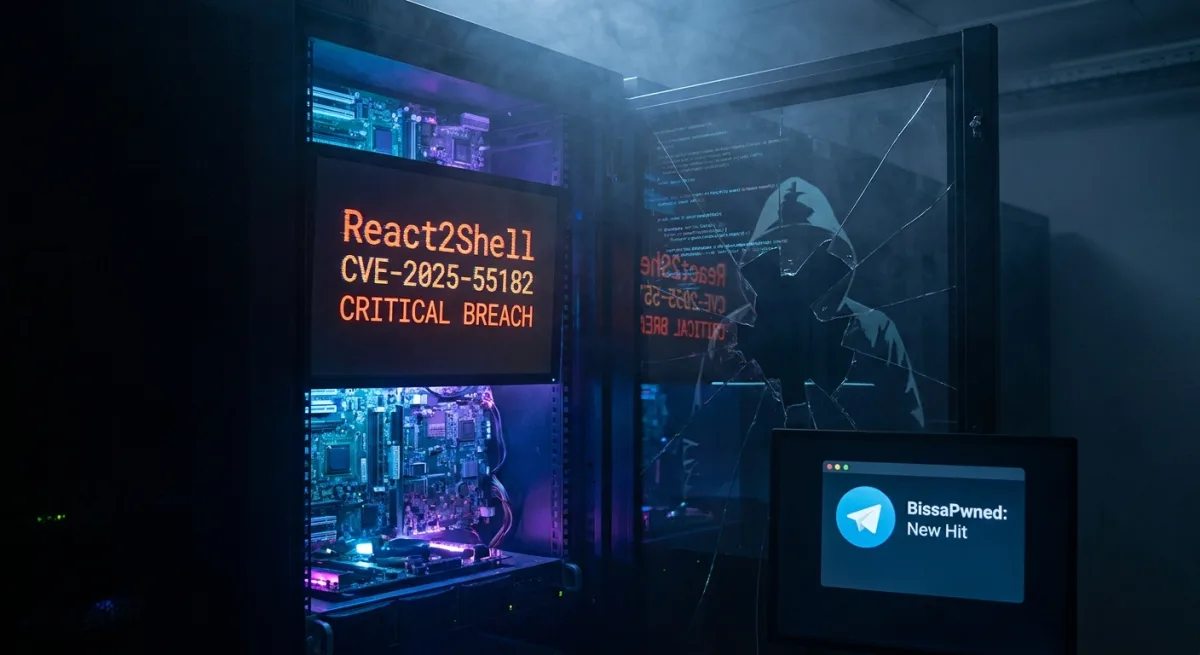
Investigators discovered an exposed server connected to the Bissa scanner platform, which is designed for multi-victim exploitation and validation. At the core of this campaign is CVE-2025-55182, a maximum severity 10.0 CVSS pre-authentication remote code execution flaw. This vulnerability allows attackers to execute code via a single HTTP request, leading to a highly successful hit rate against unpatched environments.
AI Integration and the Bissa Scanner
The exposed host contained over 13,000 files across more than 150 directories, revealing a highly organized operation focused on credential harvesting. The attackers tightly integrated AI tools like Claude Code and OpenClaw into their workflow to review code, troubleshoot issues, and refine their data collection pipeline. Transcripts showed the operator actively prompting the AI to debug lease flows and improve the scanner's performance.
OpenClaw logs also exposed a local AI-control surface featuring a WebSocket gateway, browser control, and a model pool that included claude-sonnet-4-6. The exploitation of the React2Shell vulnerability was heavily optimized to hunt for sensitive secrets. The automated system specifically targeted.env files, cloud metadata, Kubernetes service accounts, local credential stores, and cryptocurrency wallets.
Telegram Bots as Command and Control
The operation utilized a sophisticated Telegram-based alerting layer to manage the massive influx of stolen data. Runner scripts embedded a Telegram bot token for an account named BissaPwned, which forwarded notifications directly to a private chat. This setup allowed a single operator, using the alias Dr. Tube, to monitor the entire campaign from their mobile device.
Each time the bot registered a confirmed hit, it sent an emoji-delimited message summarizing the victim's identity, privilege level, cloud posture, and accessible secrets. The scanner batched the stolen.env files into ZIP archives and uploaded them to S3-compatible Filebase storage buckets. Analysts counted over 400 environment-batch archives containing more than 30,000 distinct filenames collected over an 11-day period.
Massive Credential Haul Across Major Platforms
The stolen secrets impacted nearly every major software-as-a-service tier, exposing a staggering amount of corporate data. Affected AI providers included Anthropic, Google, OpenAI, Mistral, OpenRouter, Groq, Replicate, DeepSeek, and HuggingFace. The breach also compromised cloud platforms such as AWS, Azure, Cloudflare, Google Cloud, DigitalOcean, and Alchemy.
Financial and communication services were heavily targeted, with stolen credentials linked to Stripe, PayPal, Shopify, Square, Plaid, Twilio, SendGrid, Telegram, Resend, Vonage, and Postmark. Databases like Supabase and MongoDB, alongside collaboration platforms including GitHub, Auth0, Okta, Clerk, and Slack, were also found in the credential haul. Beyond API keys, the server hosted sensitive business records, including tax documents, Oracle Fusion exports, HRIS payroll data, and stablecoin payment information.
How to Protect Your Infrastructure
Given the severity of the React2Shell vulnerability and the automated nature of these attacks, immediate defensive action is required. Security teams must assume that any exposed, unpatched Next.js or React Server Components environment has already been scanned and potentially compromised. Implement the following mitigation strategies immediately:
- Patch all React2Shell-affected stacks rapidly to close the initial access vector.
- Move all production credentials and API keys into secure, managed secret stores.
- Shrink your blast radius by enforcing tight identity and Role-Based Access Control (RBAC) policies.
- Monitor network egress traffic specifically targeting external storage and messaging APIs.
- Aggressively rotate any potentially leaked keys and implement detection mechanisms for their unauthorized use.
The Shift Toward Automated Cybercrime
The integration of AI models and Telegram bots into this exploitation pipeline represents a dangerous evolution in cybercrime. By leveraging tools like Claude Code to debug and optimize the Bissa scanner, a single operator was able to manage an enterprise-scale attack that compromised over 900 companies. This level of automation drastically lowers the barrier to entry while maximizing the operational efficiency of threat actors.
Furthermore, the immediate triage capabilities provided by the Telegram bot allowed the attacker to prioritize high-value targets in finance and cryptocurrency instantly. The sheer volume of credentials harvested from top-tier platforms like AWS, OpenAI, and Stripe highlights the catastrophic impact of a 10.0 CVSS vulnerability. As attackers continue to refine their AI-assisted workflows, organizations must pivot from reactive patching to proactive secret management to survive these rapid-fire campaigns.