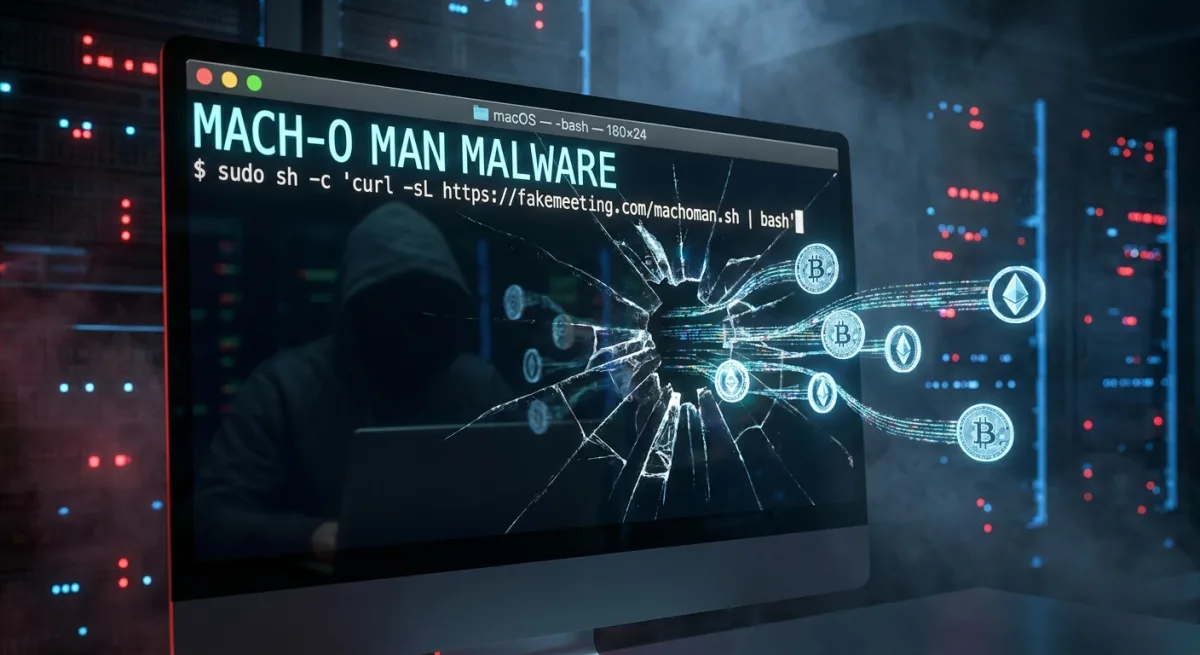
The new Mach-O Man malware is actively compromising macOS systems across the cryptocurrency and fintech sectors, turning routine business calls into devastating security breaches. Orchestrated by North Korea's notorious Lazarus Group, this sophisticated campaign bypasses traditional security controls by tricking executives into handing over direct access to corporate networks and financial resources.
According to Natalie Newson, a senior blockchain security researcher at CertiK, the Lazarus Group operates with the scale and speed of a state-directed financial institution. In just the past two weeks, these hackers have siphoned over $500 million through exploits targeting Drift and KelpDAO. The collective, which has amassed an estimated $6.7 billion in stolen funds since 2017, utilizes native Mach-O binaries specifically tailored for Apple environments where high-value crypto operations frequently take place.
The operation relies on a highly effective social engineering technique known as ClickFix. Mauro Eldritch, founder of threat intelligence firm BCA Ltd., explains that attackers send urgent meeting invitations via Telegram for platforms like Zoom, Microsoft Teams, or Google Meet. These links direct victims to convincing fake websites that simulate a connection issue. The site then instructs the user to copy and paste a specific command into their Mac terminal to resolve the problem.
By executing the command, victims unknowingly grant attackers immediate access to SaaS platforms and internal systems. Security threat researcher Vladimir S. noted on X that there are several variations of this attack, including hijacking decentralized finance (DeFi) project domains and replacing them with fake Cloudflare verification prompts. Because the malware often erases itself after the breach, victims rarely realize they have been compromised until the financial damage is already done.
How to Protect Your Systems from ClickFix Attacks
- Never paste unfamiliar commands into the macOS terminal, especially if prompted by a meeting link or a website verification page.
- Verify the authenticity of urgent meeting requests sent over Telegram or other messaging apps by contacting the sender through a secondary, official channel.
- Scrutinize URLs for Zoom, Microsoft Teams, and Google Meet invitations to ensure they are not spoofed domains.
- Educate team members on the mechanics of social engineering, as traditional antivirus software often fails to detect user-initiated terminal commands.
The Looming Quantum Threat to Blockchain Encryption
Beyond immediate malware threats, the industry is also facing long-term cryptographic challenges. A recent 50-page report backed by Coinbase warns that while current blockchains remain secure, the development of a fault-tolerant quantum computer could eventually break widely used encryption standards. Although post-quantum solutions exist, transitioning major ecosystems like Ethereum and Solana will be complex and costly, requiring preparation to begin immediately.
The Shift Toward Weaponized Social Engineering
The deployment of the Mach-O Man toolkit highlights a critical evolution in state-sponsored cybercrime. Lazarus Group is no longer relying solely on brute-force attacks or complex smart contract exploits; they are weaponizing human psychology. By targeting the daily operational habits of executives - such as joining urgent video calls - they bypass millions of dollars in enterprise security infrastructure with a single pasted command.
The staggering $500 million stolen from Drift and KelpDAO in a single month proves that the crypto industry must treat these actors as persistent, institutional-grade threats. As long as high-value targets remain susceptible to simulated IT issues, attackers will continue to exploit the weakest link in the security chain: the user.