Cybersecurity researchers at ClearSky have uncovered a sophisticated Russian campaign targeting Ukrainian entities with the newly identified BadPaw and MeowMeow malware families. This attack chain leverages highly evasive techniques to establish long-term persistence within compromised networks while avoiding automated detection.
For enterprise security teams and government IT administrators, understanding this specific infection chain is critical for updating threat intelligence and defending against state-sponsored espionage. The campaign specifically exploits border crossing appeals to deceive victims into executing malicious payloads, making awareness of these social engineering tactics essential for frontline defense.
This operation highlights the ongoing cyber warfare accompanying geopolitical conflicts, demonstrating how advanced persistent threats (APTs) continuously refine their evasion tactics. By utilizing commercial obfuscation tools and strict environmental checks, the attackers aim to bypass modern endpoint protections and maintain stealthy access to sensitive data.
The Infection Chain and Evasion Tactics
The attack begins with a targeted phishing email sent via the Ukrainian provider ukr[.]net, a service previously abused in Russian cyber operations. The email contains a tracking pixel to notify attackers when a victim clicks, followed by a shortened URL that downloads a ZIP archive containing a disguised HTA file.
Upon execution, the HTA file displays a decoy document written in Ukrainian regarding border crossing appeals. While the victim reads the seemingly legitimate government lure, the malware silently initiates its secondary stages in the background.
To evade detection, the HTA file queries the registry key HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\InstallDate to calculate the operating system's age. If the system was installed less than ten days prior to execution, the malware terminates immediately to avoid running within automated analysis sandboxes or freshly provisioned virtual machines.
Deploying BadPaw and MeowMeow
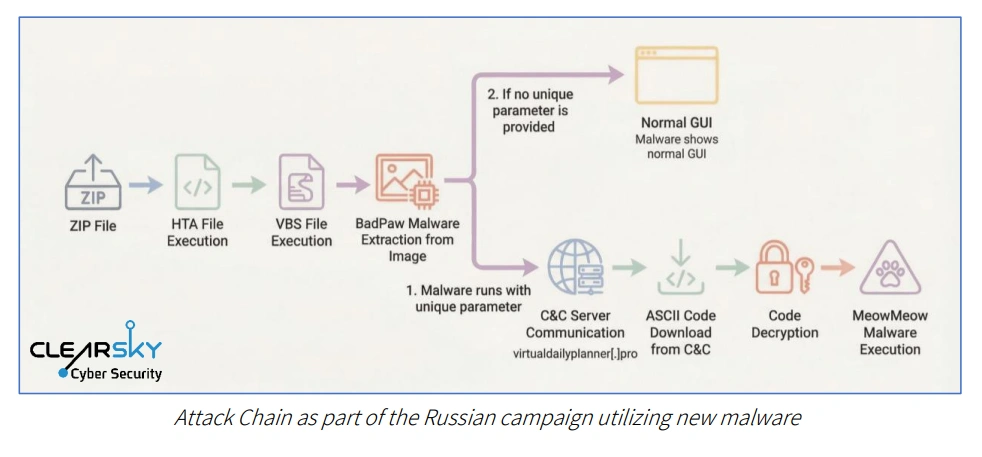
If the environmental checks pass, a VBS script uses steganography to extract hidden payload data embedded within an image. This process extracts a PE file identified as the BadPaw loader, a.NET-based tool protected by the commercial.NET Reactor packer to hinder static analysis and reverse engineering.
Once active, BadPaw establishes command-and-control communication and deploys the MeowMeow backdoor. MeowMeow conducts further environmental checks, actively scanning the system for analysis tools such as Wireshark, ProcMon, and Fiddler before executing its primary espionage functions.
| Malware Component | Primary Function | Evasion Technique |
|---|---|---|
| HTA File | Initial execution and decoy display | Checks OS install date via Registry |
| BadPaw Loader | Payload extraction and C2 communication | Obfuscated using.NET Reactor packer |
| MeowMeow Backdoor | System infiltration and data theft | Scans for Wireshark, ProcMon, and Fiddler |
Attribution to Russian APT28
ClearSky attributes the campaign with moderate to high confidence to the Russian state-sponsored group APT28. This assessment is based on the targeting footprint, the geopolitical nature of the lures, and the discovery of Russian-language strings within the malware code.
Researchers suggest these Russian artifacts indicate either an operational security (OPSEC) error or leftover development elements. The presence of a string indicating the time needed to reach an operational state implies the code was not fully localized for the Ukrainian target environment.
Frequently Asked Questions
What are BadPaw and MeowMeow?
BadPaw is a.NET-based loader used to establish initial communication with attacker servers, while MeowMeow is a sophisticated backdoor deployed subsequently to maintain persistence and facilitate espionage.
How does the malware evade detection?
The malware checks the Windows installation date to avoid sandboxes, uses the.NET Reactor packer to obfuscate code, and actively scans for network analysis tools like Wireshark and ProcMon before executing.
My Take
The deployment of BadPaw and MeowMeow underscores a significant evolution in APT28's operational tradecraft. By combining commercial obfuscators like.NET Reactor with strict environmental checkssuch as verifying the OS installation date and scanning for Wiresharkthe attackers are clearly prioritizing stealth over rapid deployment. This calculated approach suggests that state-sponsored actors are increasingly designing their payloads to survive within highly monitored enterprise environments. For defenders, this means traditional signature-based detection is no longer sufficient; proactive threat hunting and deep behavioral analysis are now mandatory components of a resilient cybersecurity posture.